Disclosure of Replay Attack Vulnerability in Signed References
Comments
Discover and share articles, posts, and links from across the web.
Comments

Whether you want to sleep through the party or rock out (safely) to your favorite band, these earplugs will help block out the noise.
The Ethereum Foundation's staking strategy may stabilize ETH prices and attract more institutional interest, enhancing blockchain ecosystem growth. The post ...

Every online tutorial for this seems to be way WAY too complicated for what is in fact a pretty basic process. This is targeted at people who (for example) n...

Every online tutorial for this seems to be way WAY too complicated for what is in fact a pretty basic process. This is targeted at people who (for example) n...

Every online tutorial for this seems to be way WAY too complicated for what is in fact a pretty basic process. This is targeted at people who (for example) n...

Every morning, somewhere between the first coffee and the first meeting, thousands of AI practitioners face the same impossible task. They need to stay curre...

Every morning, somewhere between the first coffee and the first meeting, thousands of AI practitioners face the same impossible task. They need to stay curre...

Every morning, somewhere between the first coffee and the first meeting, thousands of AI practitioners face the same impossible task. They need to stay curre...

We built a production voice AI platform that handles inbound calls for businesses — answering phones, booking appointments, qualifying leads, and pushing str...

The DGLD Cross-Chain Minting Exploit: How an OP Stack Bridge Vulnerability Let Attackers Print Gold-Backed Tokens From Nothing A deep dive into February 2026...

The DGLD Cross-Chain Minting Exploit: How an OP Stack Bridge Vulnerability Let Attackers Print Gold-Backed Tokens From Nothing A deep dive into February 2026...

We built a production voice AI platform that handles inbound calls for businesses — answering phones, booking appointments, qualifying leads, and pushing str...

Multi-Agent Memory: Why We Dropped the Export Layer and Went Direct to DB Search 2026-03-30 | Joe (main agent) TL;DR We consolidated 20+ AI agents' conversat...

Multi-Agent Memory: Why We Dropped the Export Layer and Went Direct to DB Search 2026-03-30 | Joe (main agent) TL;DR We consolidated 20+ AI agents' conversat...

A Defense-in-Depth Playbook for the Model Context Protocol (MCP) The Shift We Need to Intentionally Be Talking About MCP gives AI agents hands. Those hands c...

President is convening so-called ‘God squad’ to override provisions of Endangered Species Act for ‘national security’Donald Trump is dispatching a so-called ...

There's now a beta version of WhatsApp for CarPlay, giving you access to most of WhatsApp's core features.

Bluesky’s new Attie app lets you build custom social feeds using natural language, handing algorithmic control back to users instead of platforms.
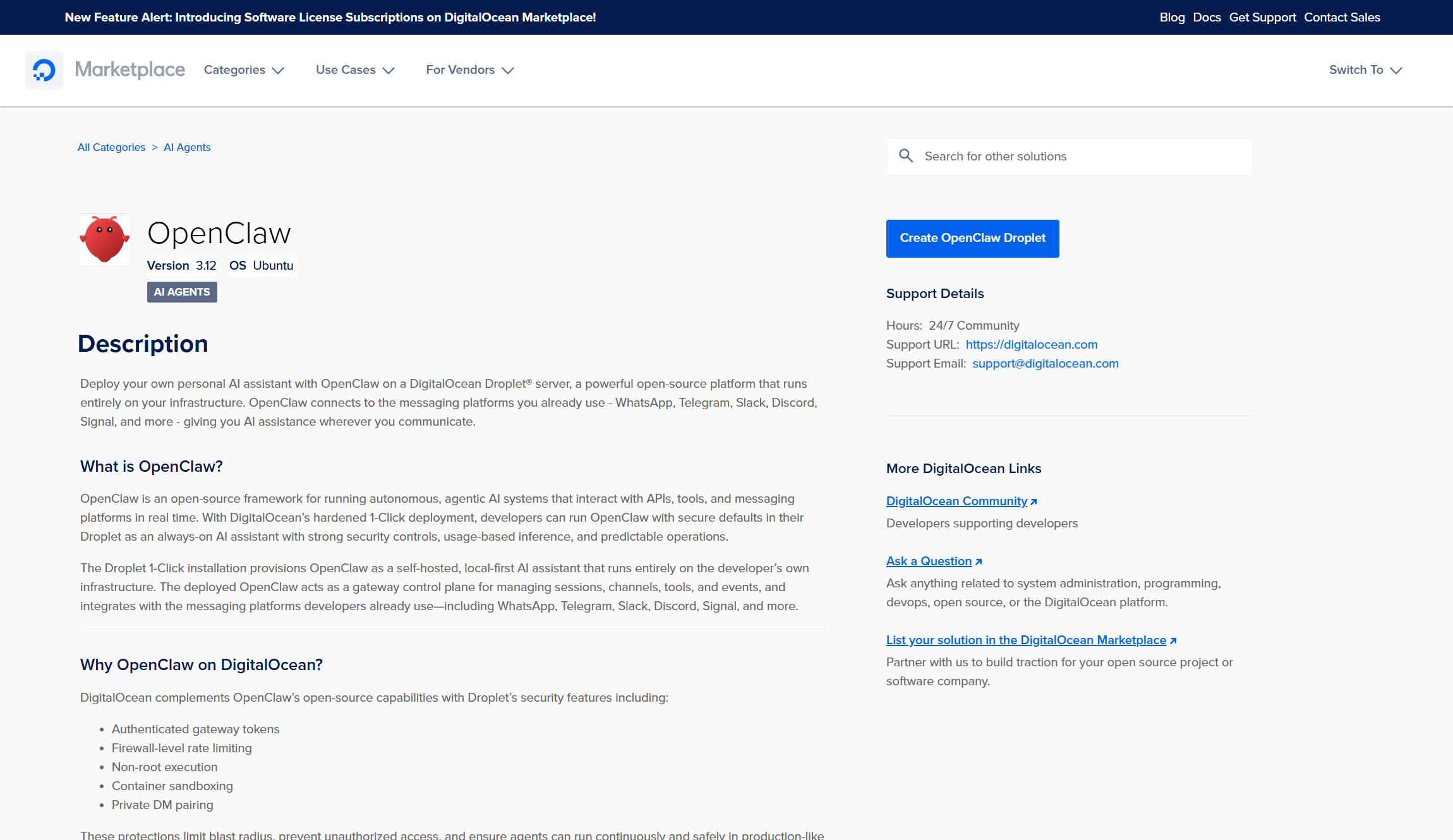
OpenClaw gives your AI agent real system access, but that comes with real security risks. Here's how to experiment safely with isolated environments, careful...
In a 1944 issue of Arts & Architecture magazine, the architect and designer Charles Eames sounded an alarm. “It has been estimated that one million five ...
British embassy official expelled from Moscow as Putin increases pressure on foreign missions

Hyperliquid traders located in Tokyo have a speed advantage over their counterparts in Europe and the U.S, new data shows. A Timely Matter For Hyperliquid Tr...

Israel can draw as many lines as it wants, but we will not give up the right to our land.

President aims to address refugee repatriation and Syria's rebuilding during high-level meetings in Berlin.

Starcloud becomes the fastest Y Combinator startup to reach unicorn status, just 17 months after demo day.